
There are always bound to be bugs in software. Sometimes these issues aren't that big, but sometimes they can be dangerous. Take for example a recent Windows WiFi vulnerability that Microsoft disclosed. This vulnerability is severe enough that it could allow hackers to remotely takeover your PC.
Microsoft recently confirmed the existence of CVE-2024-30078. This is a new WiFi attack that would allow hackers to inject malware onto your Windows computer by exploiting vulnerability in the operating system. Before you freak out, Microsoft has since managed to patch it.
By exploiting this vulnerability, hackers can inject code onto the system and requires no action from the user. This means that it could be happening without your knowledge. Companies usually disclose vulnerabilities and security flaws only after it has been patched or fixed. This is done to avoid panic where users might be worried that their devices are still open to being hacked.
Microsoft notes that they do not believe that this vulnerability has been exploited, so that's a good thing. So if you're using a Windows-based computer, you should get a notification that there is an update waiting for you. Don't put off the installation of this patch if you're hoping to prevent your PC from being hacked.

How IP address "leakage" affects personal data privacy
An IP address is like a digital fingerprint on the Internet. It is used to identify your device and its location on the network. But what happens when your IP address falls into the hands of malicious actors? How can it affect your privacy and security on the web? Let's get to the bottom of this issue and learn how to protect yourself from potential threats.
How IP address leaks occur
IP address leakage is a concept worth scrutinizing, as it has huge implications for online security and data privacy. In the age of the digital world, where every device we work with gets its own IP ID, it is important to realize that an "IP leak" can be a tangible threat to online security.
On the surface, an IP address may seem like just a set of numbers, but it's actually a key that tells a story about your activities on the Web. When an "IP" becomes visible, it opens the door to potential tracking, surveillance and invasion of your privacy. The opportunities for abuse of a "leaked" address are vast - from intrusive advertising to identity theft.
Reasons for "leaking" an IP address include:
- Malware that may be installed on your device without your knowledge;
- Vulnerable websites that fail to provide adequate levels of privacy and protection for visitors' personal data;
- messengers that are installed on virtually every phone;
- an Internet Service Provider (ISP) that may have its own security issues.
In addition, such leaks can occur when using questionable applications. Of course, using products from Melbet, 1Win and other well-known brands, the user does not experience such problems. But little-known applications, especially those downloaded from dubious places, can contain a variety of dangers, including those related to IP leakage.
What makes an IP leak particularly dangerous? It can lead to the tracking of your online activity and the violation of your privacy. Attackers can use your IP information to track your behavioral patterns: monitor the websites you visit, analyze your interests, and use it for their own purposes.
Threats to the anonymity of personal data
"Leaking" an IP address poses a number of serious threats to digital security and privacy. One of the most tangible is exposure to attacks from hackers. When an IP address becomes known to third parties, it opens the door to targeted attacks, including DDoS, the growth of which has been recorded by the FBI, which can lead to loss of access to Internet resources or disruption of gadgets.
In addition, IP address "leaks" can result in unintended disclosure of online activity. Websites and online services can use your "IP" information to track and analyze browsing patterns and behavior on the Web. This opens the door for personal data to be collected and used for targeted advertising, marketing and other third-party purposes.
Moreover, IP discovery can lead to tracking of your location, which in turn leads to privacy and security issues, especially if this information falls into unscrupulous hands.
The legal and moral side of the issue
From a legal standpoint, IP "leaks" can run into issues regarding the protection of personal information and the right to privacy. There are a number of standards governing the collection, storage and use of personal data, and "leaking" an "ipi" may result in a breach of the requirements. This may arise under data protection and privacy legislation, as well as in the context of general laws governing internet security and privacy.
From a moral perspective, "leakage" raises issues related to respect and protection of personal data. In today's digital society, where personal information plays an increasingly important role, it is important to ensure the security and confidentiality of this information. Unauthorized access to personal information, including IP address, can carry morally unacceptable consequences, such as breaches of privacy and trust, as well as misuse of personal data.
How to protect yourself
Privacy protection in today's world plays a critical role in securing and maintaining control over personal data. "IP leaks can be a serious threat to online privacy, but there are several measures you can take to help reduce their adverse impact:
- Using a virtual private network (VPN). VPN allows you to disguise your real IP address and create an encrypted connection to the Internet, thus ensuring anonymity and privacy on the Web. In this case, the "leak" of the real "IP" becomes much less likely, providing an additional level of protection of confidential information while surfing the World Wide Web.
- Use only reliable applications from well-known brands. So, downloading the Melbet here application or using applications from Mostbet, Megapari and other well-known brands, you can not be afraid of problems. But it is better to refuse from dubious software.
- Using reliable antivirus software to help detect and eliminate malicious programs, including those that may be associated with IP address disclosure, in a timely manner. Regular updates of antivirus software are also essential to ensure reliable protection against potential threats.
- You should also pay attention to the security of the websites you visit and prefer using resources that support the HTTPS protocol. This helps ensure a secure and encrypted connection between your device and the website, minimizing the risk of third parties intercepting your data.
- It is especially important to be careful when disclosing personal information on the Web. Cautions and caution regarding the disclosure of personal data further help protect your online privacy.

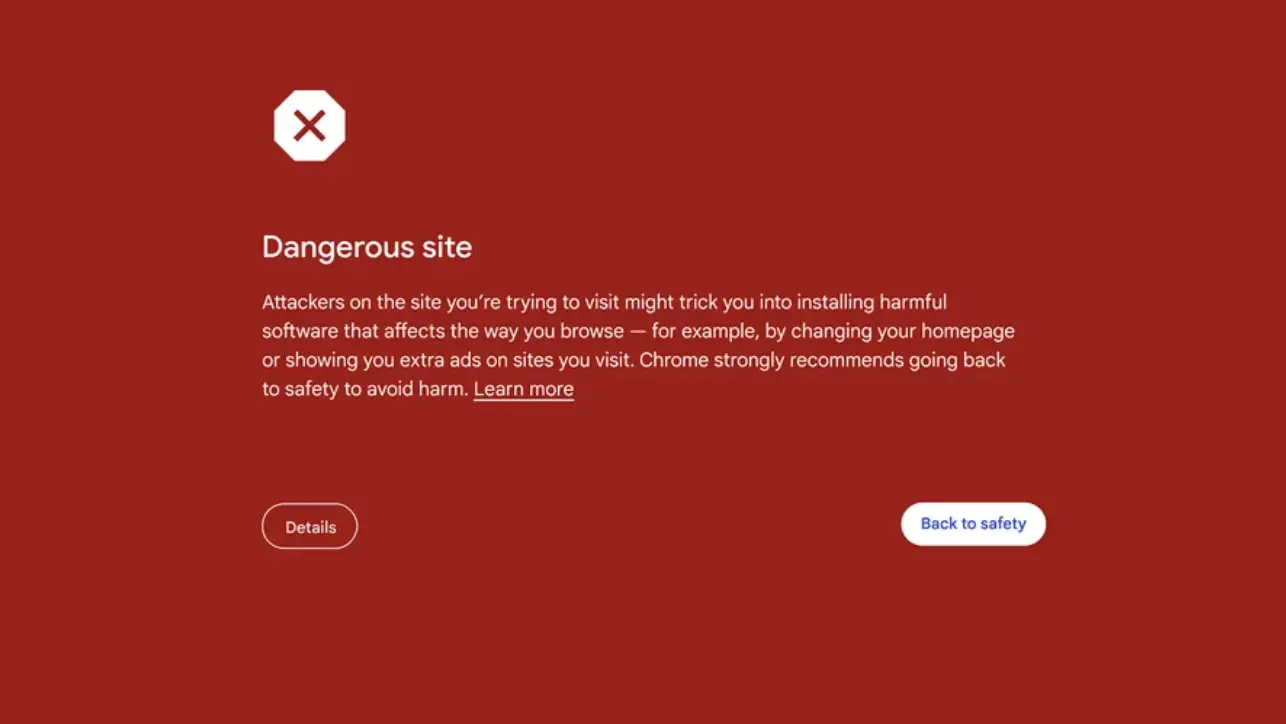
Google recently announced that it was adding some improvements to Google Chrome's built-in browsing protection for users, aimed at reducing incidents of phishing, malware, unwanted software downloads and such. The updates were announced for iOS and desktop users, and will roll out to more users soon.
To guard users against malicious sites, the Standard protection mode for Chrome on desktop and iOS will now check sites against Google's server-side list of known problem sites in real time. If Chrome suspects that a site poses a risk to a user or their device, a warning with more information will be displayed. Google adds that this should result in up to 25% more blocked phishing attempts.
For iOS devices, Google has also added new updates to Password Checkup - in addition to flagging compromised passwords, it will now flag weak and reused passwords, displaying an alert whenever it detects an issue with a password that a user has entered.
With all that being said, Google hasn't mentioned when the new updates will arrive for users with Android devices unfortunately, so users rocking an Android smartphone or tablet will have to keep an eye out for any news as to when Chrome's new safety features roll out for their respective devices.
![]()
The username and password security feature is old and dated, but it still works if you choose a strong password. It's not the most foolproof system, but it's what we've got. There are plans to potentially kill off the system with passwordless logins, like with Passkeys. Google is now making it easier for Pixel users to upgrade to Passkeys in an attempt to increase adoption.
The company has announced that they are working with various companies and online services to make the adoption of Passkeys easier. This includes companies such as Adobe, eBay, Best Buy, Uber, TikTok, PayPal, Nintendo, and more.
How does this work? Basically if you use the Google Password Manager on a Pixel phone, it will now automatically detect which accounts support Passkeys. If it detects an account that does, Google will help upgrade to Passkeys in a few taps. This takes out the guesswork of trying to figure out which services support the feature and which don't.
Passkeys are a pretty good alternative to the traditional username and password system. It works by relying on a device, like your smartphone, to authenticate your logins. Since our phones come with security features like fingerprint or facial recognition, it already makes it more secure.
Some of these partnerships should already be live, so just fire up the Google Password Manager tool to start upgrading.

Have you noticed that there are some websites that log you in automatically when you visit it? These sites rely on what are known as session cookies. These cookies contain authentication information to save you time from having to log in everytime you visit the website.
These cookies have a limited lifespan so they cannot be used indefinitely or abused, but now it seems that there are a couple of malware out there that can abuse these cookies and used to hijack your Google account. This can even happen when you log out of your account, or if your session has expired, or if you have reset your passwords.
According to a detailed report from CloudSEK and Hudson Rock, this malware needs to be installed on your desktop which will then extract and decrypt your login tokens that are stored within Chrome's local database. The malware will then send a request to a Google API which will then be able to regenerate expired Google Service cookies to maintain "persistent access" on your account.
At this point it is unclear if using 2FA will help mitigate this attack since 2FA relies on OTPs sent to another device like your phone. In the meantime, until this exploit has been patched, it's probably a good idea to avoid downloading files from unknown sources or attachments from emails from unknown and unverified senders just to be safe.
© 2023 YouMobile Inc. All rights reserved





