Search result
In an age where data security breaches and hacks are more common than ever before, it is vital to take the necessary steps to safeguard your device against external threats. Your smartphone contains all of your banking data, personal information, and your passwords, so the last thing you want is a hacker or scam artist gaining access to it. If you're looking to ringfence your phone against any and all threats, here's how to create a bulletproof Android in seven simple steps.
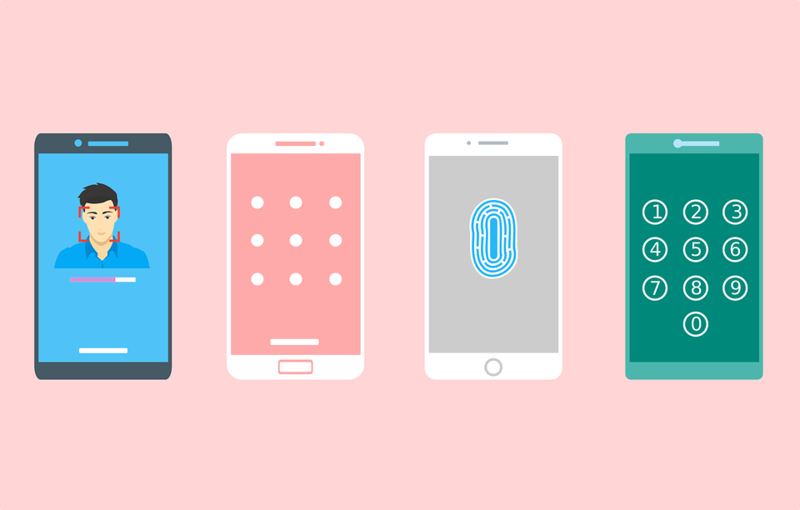
1. Password Protect Your Screen
This one might seem like an obvious one to some, but a recent study revealed that a shocking 34% of all smartphone users do nothing at all to secure their devices. A simple passcode is the first line of defense against hackers and criminals, so make sure to get one for your Android ASAP. Remember not to use an obvious passcode such as "1234" and ideally go for a pattern lock system.
2. Enable Two-Factor Google Authentification
If you're an Android user then all of your data will be synced with your Google account. This means that securing your Google account is an absolute necessity. Log into your Google account and immediately authorize 2-factor authentification (2FA) so that you'll be aware anytime someone attempts to log into your device.
3. Use a VPN, Always
A VPN app on your phone hides your IP address and prevents potential hackers from locating you and remotely accessing your device. Anyone who is serious about their Android security uses a comprehensive VPN service, so make sure to shop around for the best VPN for Android before installing one that best suits your needs.
4. Lock Your SIM
A leading cause of data breaches is straight-up phone theft. One way to make your stolen Android useless to thieves is a screen lock, while the next best thing is to lock your SIM. You'd be surprised by how much data can be retrieved from a SIM, so take the brief time to set up a PIN for your card, ideally one that is different to the PIN you use for your lock screen.
5. Disable "Unknown Sources"
Your Android has a feature in the settings which allows for the download of "unknown sources", i.e., applications that are not available on the Google Play store. This is the primary gateway for hackers to install malware onto your device, so disable this feature straight away. Chances are this strange setting is enabled by default, so double-check even if you think you don't have it switched on.
6. Install Android Antivirus
There are countless antivirus applications you can download which will run in the background without slowing your Android down. There are countless well-rated and highly secure antivirus platforms specifically for Android phones, so take a look and see which one is best for you. You can even download multiple apps if you're wanting to be extra cautious with your security.
7. Encrypt Your Data
Last but not least, the ultimate way to ensure no-one can ever get into your device is by encrypting your files and applications. Most new Android devices are encrypted by default, which makes sensitive information impossible to read or analyze, but you can go the extra mile by using a service such as CoverMe or Signal to guarantee none of your files will ever be visible.
A secure device means peace of mind. These simple steps take only a few minutes to complete, to take them now to secure your device in perpetuity.

Bitcoin is a virtual currency that uses P2P technology to carry out exchanges of value without the intervention of any bank or central body. Transactions and the issue of new Bitcoins are entirely controlled by the network. Bitcoins are the first cryptocurrency that was invented. Historically, Bitcoin is the cryptocurrency with the highest capitalization and also the highest price per single token.
Bitcoin is now a consolidated reality and although its listing on the market is subject to fluctuations even quite large from time to time, so far this virtual currency has overcome all the obstacles it has faced. Being the most traded currency, it is also quite stable although always subject to sudden changes in value compared to FIAT currencies, or the so-called traditional currencies.
The algorithm on which the BTC blockchain is based is the SHA-256 with Proof-Of-Work. Thanks to this algorithm Bitcoin can be transacted in a completely anonymous and secure way. Bitcoin accounts are in fact maintained by a public ledger and are assigned to an address, not to a person or an entity. Excluding the option to participate in their creation (an activity that has become too expensive.
The transactions involve the transfer of Bitcoin through special software that mask the complexity of the underlying blockchain: the so-called Wallets. Each wallet maintains a private key (or seed) which is used to sign the transaction by providing proof that the BTCs come from the owner of the wallet. The signature also serves to prevent the transaction from being changed by any third party who intercepts it. All transactions can then be made public among blockchain participants who usually confirm them, every 10 minutes, through a process called mining. Wealth matrix is used to earn money from bitcoin.
The mining precisely serves to confirm a transaction and also to create new Bitcoins. Mining also allows a transaction to be confirmed in a neutral way by all the computers that are part of the network, without the possibility that the blocks that make up the transactions are changed. To do this, the blockchain uses a lottery-type mechanism, which makes it very difficult for an individual or a group to control the blocks to be included in the blockchain and therefore makes the Bitcoin network very difficult to hack. It is highly recommended, especially at the beginning, the daily reading of the official forum (bitcointalk) where you can find discussions, information and news on practically every currently existing project. All this just to have a basic smattering, which is the fundamental condition for being able to operate in this world; depending on what you want to do, then, you will have to specialize in a certain sector.
How to invest in Bitcoin?
To invest in Bitcoin there are several options, some simpler and others more complex. First of all, let's start by saying that the main difference lies in the possibility of owning the Bitcoin token, or the BTC, or investing speculating on the price trend.
To own the BTC it is necessary to register on an exchange , there are more or less famous ones among which we mention eTorox , the cryptocurrency exchange of the eToro Group , which obtained the license as a regulated supplier with license number FSC1333B from the Gibraltar Financial Services Commission , i.e. the Gibraltar Financial Market Supervisory Authority.
Alternatively, you can also buy Bitcoin on the platform of the eToro broker, which has become famous in the world thanks to social trading. To join the 10 million traders present, visit the eToro website from
To invest in Bitcoin, however, it is not necessary to own the BTC and manage it through a wallet, but just relies on eToro CFD trading. To trade on this safest bitcoin broker you need to click on the link shown above. On the same platform you can choose whether to buy Bitcoin or invest on the price trend of the Bitcoin quote (BTC / USD).
Bitcoin exists because there is a network of people around the world who allow it to function, these people do it because this allows them to earn money by doing it not only allow the network to function but also certify its security and reliability.
© 2023 YouMobile Inc. All rights reserved





