Search result
Gooligan is a malware that hides within Android applications found mainly outside the Play Store, but it has recently been found that multiple apps available on the Play Store are also infected by it. The malware utilizes two vulnerabilities (Vroot and Towelroot) prevalent in pre-Marshmallow Android builds to root devices and gain access to email information, as well as authentication tokens, including those of your Google account. Gooligan then uses this unauthorized access to install applications from the Play Store itself. This of course, is done to increase the revenue associated with in-app ads. Additionally, the afflicted accounts are made to leave a 5-star review for the concerned app, without the user even being aware of what's going on.
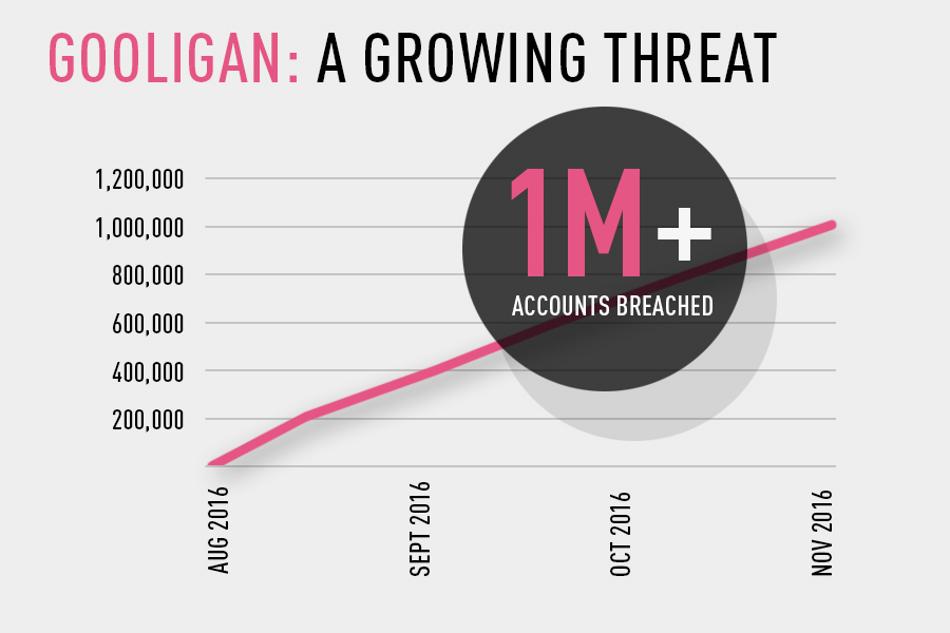
If your device is running on Android Lollipop or an even lower version of the Android OS, Gooligan can affect your device. The secret malware was found by a cyber security firm called Check Point and they have since reported that Gooligan can access Gmail, Google Photos, Google Docs, G Suite, Google Play and Google Drive on all the 1 million plus devices that it affects right now. In response to the report, Adrian Ludwig, head of Android Securities, has explained that so far, the malware, which is a variant of the previously discovered Ghost Push, has not shown any intent to steal information and has instead been only associated with promoting in-app revenue through falsified reviews and unauthorized app installations. Google has since revoked all affected tokens and has banned multiple affected apps from the Play Store.
In the words of Check Point, "Gooligan potentially affects devices on Android 4 Jelly Bean and KitKat, and 5 Lollipop, which is over 74 percent of in-market devices today. About 57 percent of these devices are located in Asia and about nine percent are in Europe,"
In order to check and see if you are affected by Gooligan, enter your email address and see for yourself at: https://gooligan.checkpoint.com/
Head over to https://forum.youmobile.org/downloads/ to find all the latest updates for your smartphone.
Saikat Kar (tech-enthusiast)

Although it's not often that we hear about Windows malware affecting Android apps, apparently, it is happening to 132 applications which were available on the Play Store. According to Palo Alto Networks security firm, all of these apps have Indonesian developers. Having said that, they also assured that in spite of the apps originating from the same geographical area, the developers are most likely not connected with each other. In fact, it is very likely that the developers are not even aware of the malware and were being victimized themselves.
The malicious code within the applications are in the form of HTML documents hidden inside other HTML documents; hailed as "tiny hidden IFrames." These documents are responsible for linking out to established harmful domains from inside the applications. If you are wondering what harm these could cause, Palo Alto explains that the malware can be used to, "modify the app's internal logic, i.e., adding rooting utility, declaring additional permissions, or dropping malicious APK file, to escalate their capabilities."
The good news is that Google has already removed these potentially harmful apps from the Play Store now.
Saikat Kar (tech-enthusiast)
Recently a security research team at ThreatFabric discovered a new Android malware that could target a list of multiple apps that requires user credentials to login including social, communication, and dating apps. The malware is called Black Rock. It is a banking Trojan - derived from the code of the existing Xerxes malware that is a known strain of the LokiBot Android trojan.
However, despite being derived from a banking Trojan, the malicious code seems to have more interest in non-financial apps than the banking apps. It pretends to be a simple Google update, and ask for permission to update the apps. Though after getting into the system, it hides its icon from the app gallery and moves the bad actors while being staying in the back.
The team found this malicious code in May, but they kept working to study it. As per the analyst team, the code can do far more than just stealing your user's login information. It can save and forward the credit card information as well. Although, it may sound like a regular malware, so far, it has acquired the ability to attack 337 apps, which is significantly higher than any of the already known malicious code. "Those ‘new' targets are mostly not related to financial institutions and are overlayed to steal credit card details," the team at ThreatFabric said in a blog post.
He malware is designed in such a way that it can overlay attacks, send, spam, and steal SMS messages. It can also lock the victim app in the launcher activity. By acting as a keylogger, it can record every key being hit and could help the hacker to gather all the information he needed. Furthermore, they have found that due to its unique nature, it can deflect the usage of antivirus software such as Avast, AVG, BitDefender, Eset, Trend Micro, Kaspersky, or McAfee.
© 2023 YouMobile Inc. All rights reserved





