Search result
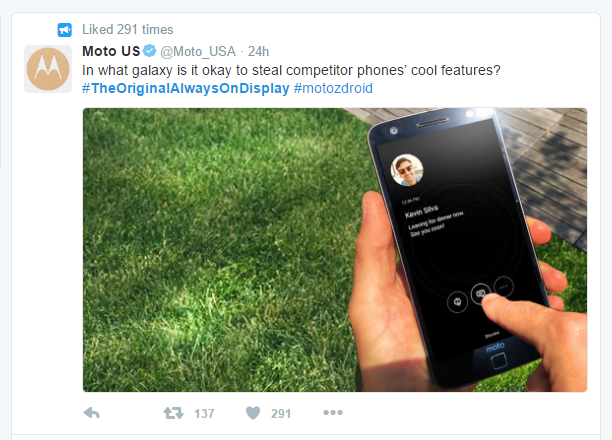
Feuds on Twitter are definitely not a new thing and according to Motorola, neither is Samsung's Always On Display or AOD. In fact, Motorola went as far as calling it stolen technology on twitter in light of the brand new Samsung Galaxy Note 7 which has the AOD feature. In their exact words, "In what galaxy is it okay to steal competitor phone's cool features?"
Apparently, they are of the opinion that Samsung stole the idea of their Always On Display from the Moto X which Motorola had unveiled more than three years ago in 2013. The Moto X 2013 had a similar feature that had been termed as the Active Display. While it can be argued whether or not Samsung had copied the idea behind its own AOD from the Active Display, Motorola was probably not right in asserting that they are the pioneers in the technology. Nokia had done it back in the year 2009 with the Nokia N86 and had again brought the technology to the fray in 2013 with the Glance Screen found on their Lumia series of Windows powered smartphones. To be frank, it is difficult to claim a particular piece of tech as your own "property" if we are to ensure advancement of the tech world as a whole.
Saikat Kar (tech-enthusiast)

A Samsung employee who is only known by his surname "Lee" at the moment, apparently was in a bad gambling debt which amounted to somewhere around $800,000! Just as any other logical person would handle a debt of that size, he decided to steal 8,474 Samsung mobile phones (which are worth a total of $711,000) from Samsung's head office in Suwon, Gyeonggi. If you have not caught on to my sarcasm yet, then let me affirm that it is indeed sarcasm and stealing from your employer or anyone else is definitely not the logical solution to any problem!
The disabled man had apparently started stealing test units meant for developers from way back in the December of 2014. In fact his operation was active till November last year; a timeframe in which he managed to steal an astounding 8,474 Samsung test units. Lee used to pawn these stolen smartphones via a used phone reseller and before long, these handsets, which were never even meant to be on sale, were being sold and used in Vietnam. As Samsung caught a whiff of the con job going on here, the matter was reported to the police. After months of investigation, Lee has finally been found and charged. Although he is clearly a reckless gambler and a thief of massive proportions, one cannot help but be amazed at the efficiency with he had run the con job for all these years without ever being caught once.
Saikat Kar (tech-enthusiast)
Recently a security research team at ThreatFabric discovered a new Android malware that could target a list of multiple apps that requires user credentials to login including social, communication, and dating apps. The malware is called Black Rock. It is a banking Trojan - derived from the code of the existing Xerxes malware that is a known strain of the LokiBot Android trojan.
However, despite being derived from a banking Trojan, the malicious code seems to have more interest in non-financial apps than the banking apps. It pretends to be a simple Google update, and ask for permission to update the apps. Though after getting into the system, it hides its icon from the app gallery and moves the bad actors while being staying in the back.
The team found this malicious code in May, but they kept working to study it. As per the analyst team, the code can do far more than just stealing your user's login information. It can save and forward the credit card information as well. Although, it may sound like a regular malware, so far, it has acquired the ability to attack 337 apps, which is significantly higher than any of the already known malicious code. "Those ‘new' targets are mostly not related to financial institutions and are overlayed to steal credit card details," the team at ThreatFabric said in a blog post.
He malware is designed in such a way that it can overlay attacks, send, spam, and steal SMS messages. It can also lock the victim app in the launcher activity. By acting as a keylogger, it can record every key being hit and could help the hacker to gather all the information he needed. Furthermore, they have found that due to its unique nature, it can deflect the usage of antivirus software such as Avast, AVG, BitDefender, Eset, Trend Micro, Kaspersky, or McAfee.
© 2023 YouMobile Inc. All rights reserved





