Why a Virus is Not the Only Dangerous Thing that Your Computer Can Catch
Why a Virus is Not the Only Dangerous Thing that Your Computer Can Catch
A malware by its simplest definition, could be defined as a piece of code that has been specifically written to cause problems for anyone who downloads/installs it on their computer. It can be a fully developed software with malicious intents, or it could be a short program, written only to hijack/damage/disrupt a specific function on the infected computer.
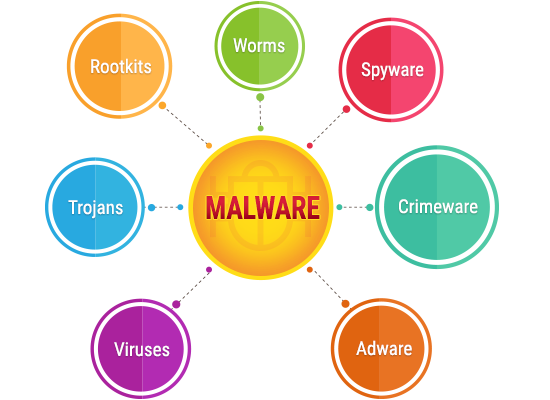
Keep in mind that malware is a very broad classificatory term which can be divided into several different types of malicious codes, based on their primary goal, medium of infection and mode of operation. A virus is just one of those multiple different types of malware, and while it can very well be the most dangerous thing that your computer can catch, it isn't the only type of malware that you should be worried about.

Understand the Threats Which a Virus Can Bring to Your Computer
Before we discuss the various other potential threats, it is imperative that we first discuss the oldest and most common type of malware first, aka a virus. Depending on the kind of infection you have, its effects may vary, and the following would be the usual suspects.
• Boot Sector Virus - The boot sector virus Infiltrates, infects and corrupts the MBR via USB/optical drives
• Resident Virus - Resides in hardware memory and cannot be removed by removing the infected file alone; also spread via physical storage/drives
• Cavity Virus - An extremely hard to notice virus that installs itself in between the gaps in the data of an installed program
• Direct Action Virus - Similar to a resident virus, it installs itself onto the hardware memory, but cannot survive without the core file
• Overwrite Virus - The primary email virus just overwrites or deletes every file it infects, making the user lose valuable information
• Multipartite Virus - Simultaneously infects and corrupts the MBR, as well as the executables
• Polymorphic Virus - The signature will be different with every single replication of a polymorphic virus, making it difficult to identify and eliminate a polymorphic infection
• Macro virus - Infects a MS Word file most often, and replaces the original macro command's execution, without changing the input

What Else Can Your Computer Catch?
Depending on the kind of sites you visit, the type of business you are in and how well your computer is/isn't protected online and offline, you could be looking at any one or possibly multiple of the following malware infections which are not classified as viruses, but can be just as, if not even more dangerous than the average computer virus.
• Trojan horse - Steals information and acts like a beneficial software
• Worm - Corrupts and deletes everything it comes in contact with, including the critical OS files necessary to run the specific OS
• Spyware - Tracks and spies on your online and offline activities
• Malicious adware - Adware designed to show ads that lead to malicious pages
• Ransomware - hijacks your computer and asks for a ransom to let you gain access back to your own data
• Fileless malware - A fileless malware has no file of its own but infects and uses genuine, installed program files to execute malicious commands
• Rootkits - Rootkits act as a restrictive barrier which protects a virus from both discovery and elimination
• Keyloggers - A spyware that logs and sends out information regarding all your keypresses (passwords, credit card data, bank data, etc. could be stolen easily)
• Malware bots - Takes over the infected computers and every infected computer might act as a hive mind, forming a botnet

What about Phishing and Spear Phishing?
In order to land on a phishing page, the user must make one of the two following mistakes:
1. Type in the wrong URL
2. Click on a link from a non-verified source
It should be noted that while phishing is an extremely dangerous threat to your online safety on any unprotected computer, it cannot be categorized as a malware. Phishing and spear phishing attacks do not infect a computer, but leads the user to a malicious page designed to replicate a universally/personally trusted website. The objective of all phishing attempts is to steal sensitive and valuable data from the user, which may include but is not limited to:
- Usernames and passwords used on the very site that the phishing page is replicating
- Other usernames and passwords used on related/unrelated websites
- Contact details and address information
- Financial information such as asset records
- One Time Passwords (OTP)
- Bank account numbers
- Other bank details
- Debit/credit card numbers
- CVC numbers
- Social security numbers
To avoid such a mishap, always check the URL for spelling mistakes or any difference in the link's structure, as compared to the genuine link, before entering sensitive information. Also, never click on an unverified link. Spear phishing uses personal information that is extremely likely to be considered as relevant by the specific individual/organization targeted. The attacker will be using personal information to make you believe in the authenticity of their email/message, all in the hope of making you click on that phishing link. Even the page where you land could have sensitive information on it, that they have likely stolen by using a malware already.
Can We Truly Protect Our Computers and Personal/Financial Information from Online Threats?
The answer is yes, we can keep our computers and our personal data protected from online and even physical media related threats because the solution is quite straightforward. Get complete web protection from one of the top antimalware developers such as Norton, McAfee or Kaspersky and keep all your devices protected against malware and phishing attempts. Thanks to massive discount coupons easily available online, this can be more affordable than you think. Without the discounts though, total antimalware protection can become a bit costly to keep up with, especially if you have multiple devices, which most of us do.
In spite of how dangerous it might be for us to use the internet today, the top antivirus and overall antimalware software providers are more than capable of handling nearly every kind of cyber threat out there, including zero-day attacks. That being said, every now and then, a malware does come around which infiltrates the defenses of even enterprise grade antimalware programs. Such instances are pretty rare though and patches are developed almost immediately after a few initial infiltrations, which stops the spread quickly.
There is a popular myth that Macs are not susceptible to malware, so anyone who believes that is advised to check for information regarding the ThiefQuest ransomware to know better. Keep all your installed programs updated, including your antivirus software to stay protected at all times, irrespective of the OS. Don't forget to enable browser protection as well, which should come by default with any of the top antivirus software solutions to keep you safe from infected sites and phishing pages.
Finally, just in case you are still using a pirated version of Windows, or a genuine copy of now-defunct Windows XP, buy an original key and update your PC immediately. Most of the time, pirated Operating Systems come with their own embedded malware, and even the versions that do not, cannot be updated. What all this means is that if the OS itself is pirated; nothing can save a computer running a pirated OS from becoming infected.
© 2023 YouMobile Inc. All rights reserved





