Search result

Image: Pexels
Cybercriminals have become huge stumbling blocks for business owners. They've been stealing assets and customer identities from companies, interfering operations, and inflicting other forms of damage.
In 2020, we can only expect cybercriminals to continue being as relentless and consistent with their attacks.
If your IT network is defenseless, you can easily fall prey to their ploys and suffer major losses.
And so the question becomes, how on earth are we supposed to protect our business?
The answer... Cyber Essentials.
If you're not familiar with Cyber Essentials, it's a data security accreditation program the UK government set for businesses and websites.
The government launched the Cyber Essentials framework to encourage organizations from various industries to bolster their IT defenses and guard their data and networks.
To understand Cyber Essentials better, let's talk about some of the biggest breaches and threats, as well as the program's strategies to keep cyber crimes at bay in 2020.
Famous Breaches
Thousands of data breaches have occurred within the decade. Many of these cases remained discreet and unreported, and some caught worldwide public attention.
Yahoo, for one, suffered multiple hacking incidents for four years, including these among the largest and most famous breaches.
The hackers, though, behaved differently in the breaches that took place for specific years.
In 2012, two separate hijackers broke into Yahoo's online infrastructure but didn't take anything. Hackers then stole records from all accounts, summing to about three billion, in 2013.
The year after, cybercriminals targeted the user database which involved around 500 million holders.
Reports say they obtained account details like people's names, passwords, email addresses, birthdays, and phone numbers.
These multiple breaches resulted in Yahoo agreeing for a settlement of almost 118 million dollars in April 2019.

Because of a software glitch or API bug, Google+ also experienced breaches from 2015 to 2018, compromising data of around 52 million users.
Due to the repeated instances, Google declared closing down Google+ permanently in April 2019.
While cybercriminals have hijacked mostly email and social media accounts, they targeted something more advanced in 2019, proving their makings of bringing far greater danger.
They exposed passwords and biometrics of a million users of BioStar 2, a web-based, open, and integrated security platform with access control, time, and attendance functionalities.
The hijackers launched a cloud vulnerability attack to leak data containing users' fingerprints and photos, which researchers discovered were unencrypted.
This incident is riskier because while you can replace passwords and ID numbers, you can't change your biomarkers, which are permanent.
Once hackers acquire your DNA prints, who knows how they can exploit them for identity fraud, profit, and other motives.
Prominent and Emerging Threats Ensue
Hackers can unleash a wide array of cyber threats and attacks to carry out data breaches.
Many of these crimes have become prominent for repetitively affecting various victims, whether individuals or small and established companies.
Ransomware, a type of malware, for instance, has nastily hit thousands, even millions, of organizations. It locks your data, threatening to delete it until and unless you pay the hacker.
Cyber hijackers also frequently launch malware through many attacks, like phishing, one of the most prevalent social engineering methods deceiving you into exposing critical information.
Hackers usually do that through official-seeming emails that ask you to access malicious links or attached files, or provide personal data to receive a prize, see fake log-in alerts, etc.

They can even inject malware through malicious or fake advertising, often in the form of pop-ups with celebrity scandals, pornographic content, or too-good-to-be-true prizes.
If you access public WiFi often, you can be at risk of man-in-the-middle (MITM) attacks where hackers can intercept your private emails and chats and send replies as if it's you or the other person.
Cyber crimes then have even advanced as hackers leverage cutting-edge technologies.
One modern onslaught, for example, is formjacking. This happens when hackers insert a piece of code onto your ecommerce site to steal private details of your customers filling in your forms.
Another is cryptojacking. Here, cybercriminals infect your site or online ads, or trick you into clicking malicious links with codes that let them mine cryptocurrencies from your device.
Now if you're a company executive, you can be a victim of whaling, a social engineering scheme asking you to authorize invoices and money transfer.
Chatbots can even become malicious when cybercriminals hack them and implant malware. They can also make one, release it, and mimic legitimate business chatbots.
Thus, with these and other prominent threats still ensuing, plus new ones emerging in 2020, Cyber Essentials can serve as your main defense mechanism.
Your Primary Defense
Cyber Essentials empowers you to bolster your IT security through rock-solid techniques you must actively and continually implement.
For one, it emphasizes that you install and periodically update your anti-virus and anti-malware software, as well as firewalls, which act as your first defense layers.
These programs can block malicious code, spam, viruses, and other suspicious activities from permeating your IT environment.
Updating these patches also enables them to detect new advanced forms of viruses, malware, and other risks.
This step is crucial because hackers can exploit vulnerabilities in your configurations in your web app firewalls and others.
Such was the case for the infamous Capital One breach, affecting 106 million users in the US and Canada and making it one of the most massive incidents ever.
Human error also accounts for a noteworthy percentage of breaches. Hence, it's crucial that you educate your staff on phishing, other deceptive tactics, and the proper responsive measures.
The Yahoo data breach, after all, happened because the phishing scheme worked.
Security configuration through tested and proven practices is also vital, like creating stronger passwords, encrypting your email domains and website, authenticating log-ins, etc.
If you have an ecommerce store and you use plugins, you should be careful, too, and install only the legitimate ones.
For example, if you're on Shopify, you can stick to browsing only among the best Shopify apps, those with high scores, excellent reviews, and other safety-verifying indicators.
Fake plugins can look official and secure but carry harmful components without your knowing.
Finally, you must establish access governance controls, authorizing only the personnel with directly related jobs to obtain specific types of company data.
If or when you experience data breaches, access control will help you more easily probe into and reinforce accountability for information management.
Making Cyber Essentials Your 2020 Priority
The Cyber Essentials program is a rock-solid defense mechanism your business would do well to invest in.
When implemented, the scheme can improve your chances of winning against cybercrimes or experiencing only little damage.
Besides your data, you also protect your sales, customers' trust, brand image, competitive edge, and more.
That said, this 2020, make Cyber Essentials your priority and successfully keep cybercrimes at bay.
Did you find this post useful? Share this with your colleagues then. Cheers!

Black Friday was a shopping extravaganza as usual, with customers spending billions of dollars on electronics alone. Even though Black Friday came and went, Cyber Monday is finally upon us with much of the same awesome deals, but from the comfort of your home and your laptop. Let's now take a look at some of the best deals on the S7 and S7 Edge that the online shops have for you today.
1. You will get a $250 gift card if you buy a Samsung Galaxy S7 or S7 Edge on an AT&T plan from BestBuy. Just for good measure, they are also throwing in a Gear VR headset and content from the Occulus Store that's worth $50, without any extra charge.
2. BestBuy also has the Galaxy S7 and the Galaxy S7 Edge from Verizon and Sprint, opting for which will entitle you to a $400 gift card from BestBuy, as well as the bundled Gear VR headset.
3. If you are the type of person who would prefer an unlocked version, then we have good news for you as well. BestBuy has the Galaxy S7 Edge (Gold and Titanium Silver) listed at $649.99, which is a whole $120 less than the usual price tag of $769.99.
4. Target will give a $250/$100 gift card and a free Gear VR headset to each customer that purchases a Galaxy S7/S7 Edge from them. The customers will also get an additional discount of 15% on their purchase while checking out from the site.
5. You can buy the unlocked Galaxy S7 international version from Amazon at $523.62.
These are the top deals on the two flagship devices this Cyber Monday and remember that they are only applicable as long as stocks last.

Earlier today, Google posted teaser tweets from its Nexus and Android Twitter accounts implying the likelihood of the commencing of Black Friday deals. At that time, little information was available about what would be announced or even when it would be announced as Black Friday is still a couple of days away. In Spite of including the Nexus Twitter account for the teasing, it was assumed that there is a possibility that hardware sales might be announced.
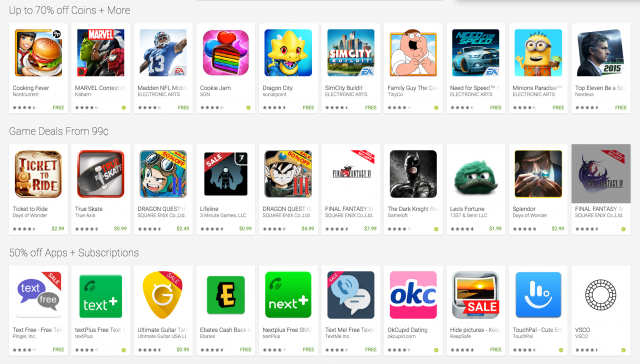
When it comes to the offers, it seems like there are deals spanning across every category you would expect on the Play Store and with so many titles being listed, it's not possible to post all the detail here. But, to give a zist, there are games starting from 99 cents, "Amazing Music Deals", movies to buy from $5.99, "Hot TV Offers", Magazines from 99 cents, 50-percent off subscriptions, up to 70-percent off Coins and a whole lot more. The Amazing Music Deals is quite interesting as you can grab some albums for only 99 cents.
It is pretty much evident that this sale is not quite the 25-cent sale we saw in previous years, so we were a little disappointed. But at least,
consumers can still save some money, especially if there is some Google Play credits laying around. So go through Google's virtual store shelves and see if there's anything that you like. To view all of the deals, click on the link below:

Technology has grown to occupy a central place in society and play a key part in all our lives. Of course, some technologies are more common in everyday life than others and have a significant impact on how we live. Mobile tech is a great example of this. Smartphones are something that we all rely on now. Whether it is making calls, catching up on emails or surfing the web, these devices are crucial to most people around the world.
The variety of things we do via mobile devices now means that the security features they contain are more crucial than ever. This includes examples such as facial recognition software, which ensures that only the right person can access a device, and mobile network security, which keeps hackers at bay.
This kind of security is essential for mobile devices, as they contain so much of our personal data, banking details, email messages and private photos. If these kinds of things were not available, people would not be as comfortable using them and they would not protect users in the best way.
The importance of secure coding practices for mobile apps
When it comes to making mobile phones safe for people to use, secure coding practices are also something that prove invaluable. This refers to mobile app developers using techniques when coding their applications that make them extra safe to use.
As apps are popular with all mobile phone users, producing those that are coded in an ultra-secure way makes sense. This not only makes it harder for online criminals to breach app security but also gives people full confidence that the apps they use are secure.
Cyber security specialists and secure coding practices for mobile
The seriousness of security for mobile devices is causing people to predict that the cyber security students of today will be at the forefront of the sector moving ahead. This is because these students learn not only what common online dangers pose most problems to mobile users, but also which security weaknesses hackers might target in an app or mobile phone.
They can then use this knowledge to design mobile devices that provide much stronger protection against hackers and apps that utilize the latest secure coding practices to deter online criminals. In terms of mobile apps in particular, techniques developed around secure coding within cyber security can be directly transferrable to creating safer applications.
How do you become a cyber security specialist?
The above shows that training to become a specialist in cyber security could lead to decent employment opportunities in the mobile sector. As things such as secure coding practices become more important in mobile phone apps, people with specific skills in this area are in demand.
The online nature of modern society also means that people with in-depth knowledge of online security are in demand across a range of other industries. This can be businesses in any sector that have an online presence and need someone who can safeguard their network, protect their databases and help them work securely in the cloud.
Due to this, training to work in cyber security is a popular career choice.
If you are wondering how to become a cyber security specialist, the best place to start is getting the right qualifications. The Master of Science in Cybersecurity from St. Bonaventure University is a popular course in this field and perfect if you like the flexibility of online studies. This program teaches students all they need to know about helping businesses stay safe from online threats. This includes learning around secure coding practices, cloud security, machine learning and data mining.
What skills do you need to work in cyber security?
Cyber security is a field where academic qualifications are not the only driver of success. If you plan to move into this employment sector to build secure apps or make mobile phones such as the Apple 1Phone 14 Pro safer, you also need the right skills to call on.
The most important ones for specialists in this sector include:
- High-level IT/computer skills
- Problem-solving
- Communication
- Organizational skills
- Multi-tasking
- Leadership
- Programming
- Analytical skills
- People skills
Although the above list does not show every single skill that can help you succeed in cyber security, it gives a flavor of those that are used most regularly in roles across the industry. By working on these skills, you can not only succeed in your career post-graduation but also become more attractive to potential employers.
What type of person should move into cyber security as a career?
People who are interested in computers, technology and online/mobile tech are all ideal candidates for this sort of career. This sector can also be a good fit for anyone who loves to work independently at times and use their knowledge of IT to solve cyber security issues. This could involve building impenetrable digital fortresses to keep out hackers or enjoying the thrill of responding effectively to a sudden online threat.
Of course, if you already work in IT or other fields based in computer science, then you may also find working in cyber security interesting. It is key for all cyber security professionals to enjoy keeping up to date with the latest industry trends (such as secure coding practices) and emerging online dangers. This enables them to use this knowledge in their own role and fulfill their duties effectively.
What roles do specialists in cyber security typically move into?
Cyber security is actually a wide-ranging term. There is a great range of individual roles within the sector that people can move into. These include:
- Security architect
- Network engineer
- App developer
- Solutions architect
- Lead software security engineer
- Information security analyst
- Chief information security officer
When it comes to cyber security for mobile phones in particular, app developer is one specific role that stands out for graduates. If you like the thought of helping to design apps that are ultra-secure, then it could be the perfect job for you. Secure coding practices that cyber specialists develop are crucial to working in this position and creating robust apps.
But how do cyber security experts develop these types of coding practice?
Security testing
Although there are multiple ways that specialists in cyber security develop secure coding practices for mobile apps, a focus on security testing is one of the most important. This refers to mobile applications being thoroughly tested to ensure that they are safe to use and provide excellent security against hackers.
By doing this, the app developers are able to code products that have been properly tested for high-end user security and products they feel confident are secure to use on a global scale. Security testing also enables those involved with mobile app development to spot any glaring security errors in the product’s coding and across the application in general.
A good example of this would be performing periodic vulnerability scans on the app in order to identify code that might be vulnerable to attack. It is also possible to use automated source code analysis to spot any security flaws in an app’s coding.
Security patches to fix coding issues
It is crucial to point out that there may not have been any security issues with an app before it was rolled out. However, there are always new online threats emerging that see hackers finding fresh ways to get past previously secure app defenses. Once this happens, it is vital for app developers to work quickly to make security patches available to users and plug any vulnerabilities.
This is something that cyber experts have helped to popularize, and they continue to work with the mobile industry to help it respond to emerging threats from online criminals. It is common for these security patches for apps to rely on amendments to code and for extra layers of security to be added into the source code of an app to make it safer. It may also involve removing code that has been exposed by hackers or that has become a security weakness.
Authentication of certificates
Authentication is another valuable technique for secure coding and creating robust mobile apps. This refers to developers using specific software in their apps to validate the contents of an online certificate. These certificates are digital documents that confirm the true identity of a website or server. The certificate itself includes key data about who issues the document and which hostnames are connected to it.
By using software such as NSURLSession or HostnameVerifier, app developers can authenticate certificate contents from users and reduce the danger of certain attacks (such as so-called man-in-the-middle attacks). These sorts of attacks can be serious, as they amend the communication between the server and the app itself. This can then enable cybercriminals to access the app’s code and make changes to it or alter certain app features. By authenticating certificates, the app becomes safe for genuine mobile users to download and is kept safe from cybercriminals.
Biometric data storage
As we have already noted, biometrics is a major trend in mobile development and enables people to use unique personal data to access tablets, smartphone and apps. Good examples of this in action include facial recognition scanning on mobile devices and fingerprint scanning. Although this data may be unique, it still needs to be stored on mobile devices and apps for them to recognize who is trying to access them.
As with any kind of data storage for sensitive information, it is key for biometric data to be safely looked after for mobile users. Cyber specialists have been instrumental in developing techniques that enable this and allow biometric data to be used safely in the mobile sector.
A good example of this is how the technique of hashing was developed in the cyber security industry to help store this sort of information safely on apps and mobile devices. This involves turning biometric data into a string of code that is hard for unauthorized people to decipher. Hashing is also widely used in the mobile world to store unique personal data, as it stops this data from being matched with other sources online to authenticate it. Code obfuscation is another widely used technique in this area that was developed by cyber experts. This sees the code structure/syntax amended to make the data complex for hackers who do not know the rationale behind these changes.
Data encryption
Another useful secure coding practice for mobile apps developed by cyber experts is data encryption. This is useful for app developers, as it allows any sensitive data stored on an app to remain safe from hackers. This is because encrypting data takes the raw user information that an app might hold and jumbles it up via a high-end computer algorithm.
This encrypted data to be stored on the app is extra secure and almost impossible for anyone without the correct encryption protocol to decrypt. As you can imagine, this technique around app safety is much better than simply storing sensitive data without any kind of encryption to protect it. If this were to happen, any hacker who did breach an app’s security features would have access to a wealth of personal user information in its rawest form.
Avoiding hardcoding of things such as APIs in the source code of an app also means that hackers cannot steal key data if they manage to obtain the application source code. When combined with cryptography in app creation, this allows developers to create products that are able to resist common threats such as side-channel attacks. As a result of the above, the app’s code is kept much safer and the data on an app is kept more secure – even if online criminals were to breach the application’s initial security features.
Authorization
A key element of mobile app safety is that only authorized users should be able to access an application. This, of course, is also something that is key for mobile devices in general, where only the owner of a tablet or smartphone should have access to it. When you think of the wealth of sensitive data on our apps and phones, this makes perfect sense.
Good practice in terms of secure coding that cyber experts have developed is therefore key for app authorization. This sees apps created in such a way that people have to sign in first and confirm their identity before being able to access them.
App authorization through secure coding on a more general scale is also interesting to note and something that cyber experts have helped to develop. This sees the code behind an app written in a way that only allows users to access certain parts of the app. As a result, it stops people getting to parts they shouldn’t have access to and unauthorized people from getting up to mischief (such as stealing data or changing the application’s code).
What’s next for cyber security within the mobile world?
There is no doubting how important online security is to the mobile sector and what a great job secure coding practices do at keeping mobile users safe. Due to this, it is almost certain that cyber security will continue to play an increasingly key role in the mobile phone industry. But how might this look as we move forward?
If we look at applications specifically, you expect that online security experts will continue to find new ways to secure the data that applications collect and store. This could involve higher levels of data encryption and new algorithms that help facilitate this.
For mobile devices in general, it would seem certain that cyber security specialists will continue to develop new techniques in areas such as secure coding to make them safer. This could involve the next generation of phones having ever more sophisticated biometric access protocols or the new wave of tablets running on network security processes that are almost impossible to breach.
Secure coding practices are key for mobile phones
People will only continue to use mobile phones if they feel that it is safe to do so and they are designed in a way that keeps online criminals at bay. One very effective method to achieve this is through the secure coding practices that cyber security specialists have developed for use with mobile devices. By developing and helping to implement these practices, cyber specialists are able to make mobile phones and apps a lot more secure to use.

Motorola is getting ready for Cyber Monday and like the other players in the tech world, showing the details of deals on the website is quite useful. Currently there are three deals listed on the website and hopefully we can expect to see additional deals in the coming Monday.
To start off, the price of Moto X (2nd Gen) 64GB has been slashed by 25% to bring down the final cost to $299 from $399. You can avail this deal from within the Moto Maker, where it lets you customize the device to your preference. Hence, the price might go up depending on the level of customizations.
Motorola will also give the Moto 360 (1st Gen) at 50% discount, bringing its price down from $299 to $149. Please take a note that this model is the 1st Gen, and at Amazon, you can purchase this device with variety of models to choose from starting at about $140.
We'll say, this deal is not so enticing and definitely doesn't stand out in Cyber Monday history. Finally, those looking to own a Moto G (2nd Gen) can get one for just $99, brought down from $179.99. That's more than 40% discount on the price listed for the phone. Then again, this is the 2nd Gen model, not the 3rd Gen which can bought from Amazon for $170.
Via: Motorola
© 2023 YouMobile Inc. All rights reserved





