Search result

AnyTrans by iMobie promises to be the only cloud management solution that you will ever need, but what is it exactly that they are offering which makes it so great? Or is it all just marketing? Let's find out in this overview of the AnyTrans cloud management software.
Easier and Faster Cloud Migration

Just like the name suggests, AnyTrans allows its users to transfer files from one cloud storage service to another seamlessly and without having to go through multiple time-consuming steps. You can move everything at once or just the files you need; it's all up to you because AnyTrans allows both options at high speeds.
Faster Upload Speed and Reduced Download Times

AnyTrans automatically makes the user's download and upload operations faster with the help of multithread technology, even when downloading or uploading in bulk. The software achieves this by maximizing the available bandwidth on your internet connection and this remains effective even when you are using multiple cloud drives at once for your download and upload operations.
Manage All Your Cloud Accounts from One Place

Even the most basic cloud users at least have two to three accounts spread out over multiple services such as Google Drive and Microsoft OneDrive to name a few. Now, it often becomes challenging to manage all your data since each service requires a different login id to access your account on their site. AnyTrans is the perfect solution here because once you link your accounts with the software, you won't have to log in separately into each service again. It will act as the central hub for all your cloud storage services.
Secure Sharing

While all cloud storage options offer sharing services, what makes AnyTrans perfect is the fact that you can use it to share any file you like from any of the linked cloud storage accounts, without having to log in and go through each interfaces separately. Sharing options include social media sites like Facebook, Twitter and Google+, or just link sharing via email or supported instant messengers. An important part of the service that AnyTrans offers is whether you are accessing, storing, downloading or sharing data from the software, everything remains private and only accessible to you.
The bottom line is that if you are someone who uses multiple cloud storage services, you are definitely going to be more productive with AnyTrans by iMobie because it makes managing everything simpler. The software is available for both Windows and macOS for download, so do try out the pre-release version. You can even access it from any web browser on any mobile phone, tablet or computer.

After a lot of speculations, leaks and rumors, the Galaxy J5 & J7 2017 are finally out as Samsung made it official yesterday. We have had enough of the rumors, but now it\'s time to take a look at the actual internals.
Display
J5 has a 5.2-inch 720p display, while the J7 has a 5.5-inch 1080p screen as expected. The good news is that both of them are AMOLED panels.
SoC and RAM
Both devices share the same Exyno 7870 14nm chips with Mali-T830 MP2 GPU. The J5 2017 only has 2GB of RAM though, but the J7 2017 has a more respectable 3 gigs of RAM.
Camera
The 13-mp rear camera sensor with f/1.9 aperture is common to both devices but the J7 also has a 13-mp front camera with flash, unlike the J5, which is stuck with a plain 5-mp shooter without any flash aid.
Battery and Price
A healthy 3,600mAh battery will be powering the J7, while the J5 will have to settle with a smaller 3,000mAh cell instead. The price difference between the two devices is basically of £60, so you would probably be much better off opting for the Galaxy J7 2017 for £340 ($440 approximately) than the Galaxy J5 2017 for £280 ($360 approximately).
Other than these, the J7 will come with USB Type-C while the J5 will be sporting the aged but more accessible micro-USB. Fingerprint scanner will be present in the usual place on both devices; i.e. just under the Home button.
Saikat Kar (tech-enthusiast)
Google released the Android N build all of a sudden last night. For the first time in Google's history developer preview edition has been released this early. The reasoning behind this is to get feedback early and release it to the OEMs in order to the help them build their flavor quickly.
Right now this build is compatible with the Nexus 6, Nexus 5X, Nexus 6P, Nexus Player, Nexus 9, and Pixel C. Given below are some of the salient features:
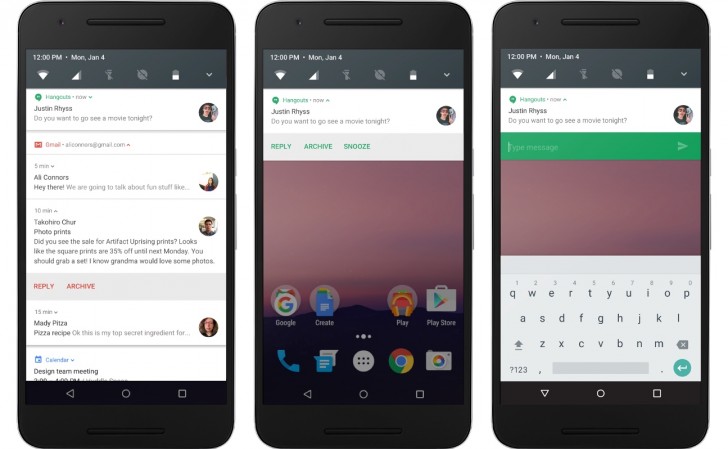
Better notifications
There will be quick shortcuts once the notifications shade is pulled down. After pulling it down, users will be able to the toggles and see a paginated grid. This essentially means there will be another page for the toggles which are not used often.
One more nice feature is the ability to reply to messages right from the notifications screen. This is something iOS does and it can be very convenient. Implementation of this feature will be the developers call but it is expected that the popular IM apps will take advantage of this new RemoteInput notifications API.
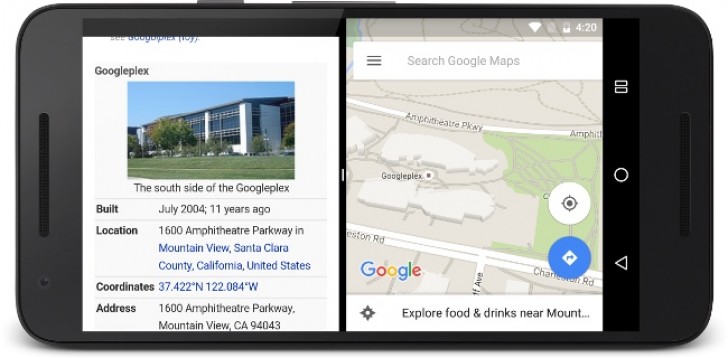
Split-screen multitasking
The split-screen multitasking can be used by pressing the overview button and dragging one of the windows to the top of the display to attach it there. Then another app can be selected in work in the rest of the screen. Another way to do this is to swipe up from the overview key to select the app to work on the half the screen and select another app for the rest.
Improved Doze and Project Svelte
Doze mode can now put hold on the background activities when the display is switched off, irrespective of whether the device is active or not. Added advantage is that there will be saving of battery charge. Now Project Svelte is in a better state and minimizes background activity by getting rid of the three default broadcasts.
Improved Settings app
The settings app will show the description of the items and there will be introduction a new option for data saving. The improved night mode will make the screen warmer for better readability.

The TSA approved eGeeTouch travel lock is a handy piece of gadget that promises to keep your luggage safe during travels, without you ever needing to memorize complex combinations. Let's now take a closer look and find out if it really is better than the traditional padlock or combination lock.
Easier Unlocking
After using it for a few days one has to appreciate the ease of unlocking the eGeeTouch padlock without the need to dial in security combinations every time you need to open the bag. It can simply be unlocked with a single tap from the right eGeeTouch NFC tag. Alternately, you can unlock it with your smartphone (Both Apple iOS and the Google Android OS are supported), as long as you are in Bluetooth or NFC range.
Enhanced Security
The Intelligent Encryption technology used by eGeeTouch makes sure that no other NFC device can be used to unlock your luggage. It uses unique code generation (out of a 100 million possible combinations!) each time you lock it. Just in case the NFC tag or the smartphone itself is lost, the user can use the eGeeTouch app to log in and remove the tag or the registered smartphone from the approved list.
TSA Compliance
The eGeeTouch is TSA compliant, which means that the TSA authorized airport personnel will be able to open and check your luggage with their master key if required, without having to break open and destroy the lock in the process.
Other Features
Some other highlights of the eGeeTouch travel lock are as follows.
· Over 3,000 open and lock cycles that should last well over 2 years on just a couple of LR44 batteries
· Color LED indicators to show open/locked status
· Battery compartment cannot be accessed while it's locked, therefore enhancing security
The eGeeTouch padlock is a fine example of technology making its way into every aspect of our lives and it's quite a good one. Made for the convenience of everyone and not just the techies, the travel lock is completely foolproof and can be used by anyone. All in all, it is indeed a better and more convenient alternative to the traditional combination locks we usually use on our luggage.

The xFyro xS2 is a pair of Bluetooth 5.0 earbuds that promises to deliver a lot of premium features like 300-hours battery life (standby), waterproofing, comfy but tight fit and of course, high quality HD sound. If you are interested in the xFyro xS2, going through the various features of the earbuds in details should provide a better idea regarding what to expect and that's why we have taken a look and prepared this overview for you.
Important Specifications
Those that know precisely what they are looking for will appreciate the following spec highlights.
· Dimensions: 6.25"L x 1"W x .75"H
· 0% to 100% charging time: 2 hours
· Use/standby time: 5 Hours/ 300 Hours
· 850mAh Power Bank and dual-port charging tube With USB and micro USB
· Built-in microphone
· 10m Bluetooth range
· IP67 Certified dust and water resistance
Now that the important specs have been listed, it's time to take a closer look at them and see how well each of these have actually been implemented in the xFyro xS2 Wireless earbuds.
IP67 Certification
While the term "waterproof" isn't exactly accurate, the xFyro xS2 does have a proper IP67 certification, which means the pair can stay submerged in water as deep as 3.3 feet, for up to 30 minutes at a stretch, as well as being dustproof. The IP67 certification makes the xFyro xS2 a perfect pair of outdoor headphones that you can use in the pool, or while trekking through rainy weather and dusty roads.
Bluetooth Range
The 10 meter or 33 feet range claimed by the company is dependable, but you have to keep in mind that in order to fully utilize this distance, the sources (yes, it supports multiple connections at once) and the headsets need to remain uncovered and unobstructed. While that is somewhat difficult as there are always walls and other obstructions, even the compromised range still remains good enough for regular needs.
Battery Life and Included Powerbank
A 5-hour usable battery life is roughly what has come to be expected from most modern wireless headsets and thankfully, the xFyro xS2 delivers on that front. The standby time is particularly impressive at 300 hours though! Just in case you do run out of charge, plug it into the case, which is also a 850mAh powerbank and it will charge the headset from 0 - 100% in hardly two hours.
Sound Quality
The main reason why anyone buys headsets is of course, the sound quality and we are happy to say that you won't be disappointed here. This is not one of those bass-heavy headsets that sacrifice clarity and quality in favor of thumping booms. Instead, the xFyro xS2 wireless earbuds takes care to deliver the highs, mids and lows with equal clarity. Make no mistake though, it can still get very loud when you need it to be, which is amplified by the excellent CVC 6.0 Noise cancellation, making the wireless earbuds useful even in loud, noisy areas, especially while taking calls with the built-in microphone.

All of this, combined with the premium aluminum build, makes the xFyro xS2 wireless earbuds an excellent proposition. It could easily replace your Apple AirPods or just about any other Bluetooth headset in the price range. If you are looking to get one, there's actually no reason to not buy it at just $125!

Online gaming sites can be a honey source for money laundering. And if casino operators slip up the chance to detect such attempts or simply lack the appropriate measures, they can have their license revoked and even face penalties.
One such illustrative example is the trendiest scandal of The Star Entertainment Group in 2022. According to Sarah Court, ASIC Deputy Chair, Star’s board and executives failed to prevent money laundering at its Sydney Casino. If in a few words, the Star Entertainment Group allowed 1,222 users to gamble over $617.6 million via high-risk payment channels. As a result, the company’s NSW license was suspended, and it was fined $62 million dollars. And similar cases are more than enough in the iGaming space.
Actually, gaming operators have much remaining on their plates that need to be done when it comes to fighting against money laundering. The most crucial thing they can do is to implement an efficient CDD (Customer Due Diligence) check and follow AML processes.
However, even these can sometimes not be enough to confront powerful hacking attacks and malicious acts. Gambling organizations first need to learn how to identify suspicious behavior and what the most common laundering schemes are to minimize the risk.
In this article, we will shed light on the 6 most used types of money laundering techniques hackers practice in online casinos. So, get comfortable and let's begin.
What Are the Most Widespread Money Laundering Schemes in Online Gaming — Top 6

When it comes to money laundering, it can take up different shapes at both KYC and withdrawal without verification casinos. Here, we have highlighted the most common ones.
#1 Cash-in, Cash-out
Probably, this is the most typical and the simplest money laundering scheme in the gambling sector. The essence of this method is as follows: a malicious actor just exchanges dirty money with casino chips in physical gambling venues or electronic money in online casinos. Then, these chips or electronic funds are used to play various casino games before the scammer cashes them out as clean money in the form of a check (in physical casinos) or online winnings (in online casinos).
As a result, dirty funds can be mistaken for money earned at a gambling site. Normally, fixed-odds betting terminals are used in this method since they let the player only lose a small amount when cashing out.
One such example is the case in 2006 when a lawyer from Virginia used this cash-in, cash-out approach to launder $250,000 at the Taj Mahal Casino in Atlantic City. To make it possible, he first transferred $250,000 embezzled money into a betting account, then purchased a casino marker with $10,000, lost $1,000, and cashed out the remaining funds.
#2 The Vancouver Model
If we go back to the time period between 2008 and 2018, we can see that gambling establishments in Vancouver were massively used to launder money in large sums from China. The reason for this was the restriction imposed on Chinese citizens, according to which they were prohibited from bringing more than $50,000 out of the country. That's when criminals in Vancouver thought of a workaround and offered it to local players.
The scheme required people to wire funds to the Chinese banking account of a Vancouver-based crime gang. Upon their arrival in Vancouver, they could get cash in exchange.
In the next step, they just needed to take this cash to a casino in Vancouver, place several small bets, and then cash it out as casino winnings. As a result, it will be cleaned of its illegal source.
#3 Collusion Between Gamers
Another money laundering strategy is the Collusion Between Players. If in simple words, it requires one gamer to intentionally “lose” their dirty money, which was exchanged for physical casino chips or electronic money beforehand, to an accomplice gamer at online or brick-and-mortar casinos, for example, in a poker game. This way, the money is no longer related to its criminal roots and can easily be withdrawn as “clean” funds.
The “advantage” of this method is that it gives launderers a chance to escape any AML detection policies, as currently, they can only be triggered by successful bets against the gambling platform itself and not other gamers.
#4 Exchanging Goods Through Gambling
This method allows a gamer to clean their funds at the same time as they receive illegal money and sell illegal goods. Simply put, both the seller of illegal goods (like weapons or drugs) and the buyer takes part in the same casino game. This way, the buyer can easily send funds to the seller through the bet or game using the player-to-player transfer option. Then, the seller cashes out the money from their payment account in exchange for goods. It is quite efficient if we look from the criminal perspective.
Technically, as funds come via gambling, they can't simply be traced as an illicit transaction.
#5 Purchasing Chips from Someone Else
The next common method of money laundering is when people try to clean their funds by buying casino chips or the winnings of other players at a higher price. For instance, the launderers can approach jackpot winners at a poker game venue and offer them cash at a premium in exchange for their winning cheques.
In some cases, these malicious actors can even pay off the gambling debts of the gamer in return for getting payments in the form of chips later.
#6 Mixing Non-Gambling and Gambling Methods
More professional criminal groups are practicing various ways to further conceal traces of funds laundered through gambling sites. They typically involve virtual assets like NFTs, cryptos or even property purchases to achieve their goal.
Simply put, criminals use their dirty money to place small bets at online casinos, which will help them clean their money and then use these funds to buy various properties. Later, they sell these properties and cash out money.
Through this method, criminal groups try to confuse authorities by masking the origin of the money.
Key Vulnerabilities in Online Casinos

Both land-based and online gambling venues are often abused by criminals to launder money. The cause of such frequent hacks lies in the security vulnerabilities that most online casino platforms come with.
Overall, according to FATF (The Financial Action Task Force), there are multiple potential vulnerabilities that gambling operators might have that result in money laundering. These cover:
- Transferring funds between customers;
- Cash payments;
- Deposit accounts;
- Third parties;
- Multiple accounts;
- Identity fraud;
- Receiving crime proceeds;
- Multiple operators.
Even though these are not the only “faulty elements” that lead to illegal activities, they are still the key ones.
In order to prevent or minimize the risk of money laundering cases, gambling operators should implement some precautionary measures. The most common ones cover:
- Utilizing customer due diligence procedures (gathering personal data, verifying the source of money, etc.);
- Integrating KYC procedures;
- Reporting suspicious transfers;
- Organizing employee training from time to time, etc.
And don't forget about the most effective method, which requires compliance with AML regulations.
© 2023 YouMobile Inc. All rights reserved






